Features
CDACSIEM Features
CDACSIEM delivers end-to-end security services that monitor, detect, and respond to cyber threats in real time. Our services combine centralized log management, intelligent threat analytics, and automated incident response to protect critical systems while maintaining strict compliance and complete data sovereignty.
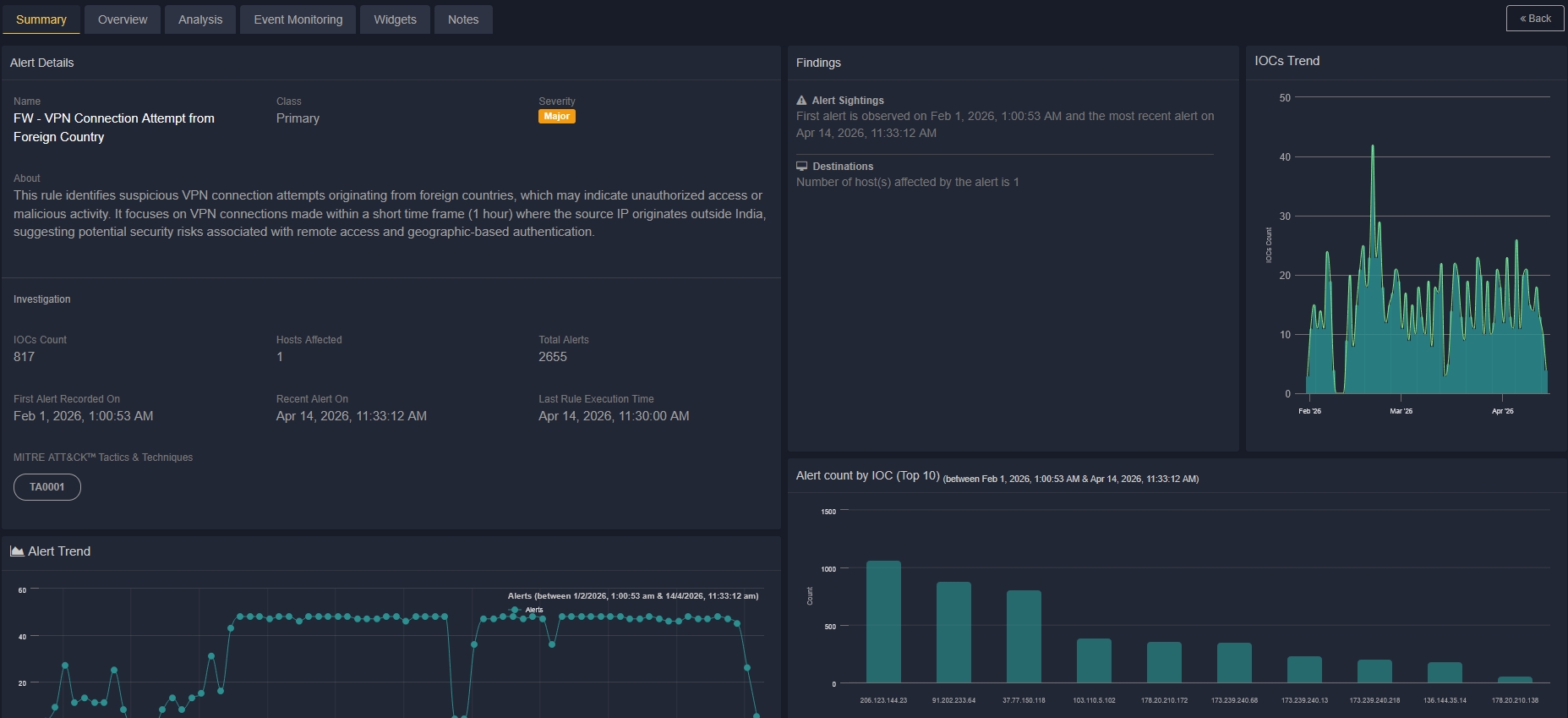
Real-Time Threat Detection
Continuously monitor security events across your entire infrastructure and detect suspicious activities as they happen using advanced analytics and behavioral monitoring.
Identify threats at an early stage with intelligent alerting, contextual insights, and prioritized notifications to significantly reduce response time and potential impact.
Advanced Event Correlation
Correlate logs and events from multiple security tools, networks, endpoints, and applications to detect sophisticated multi-stage attacks that traditional systems often miss.
Reduce alert fatigue and false positives by intelligently grouping related events into meaningful incidents, enabling faster and more accurate threat response.
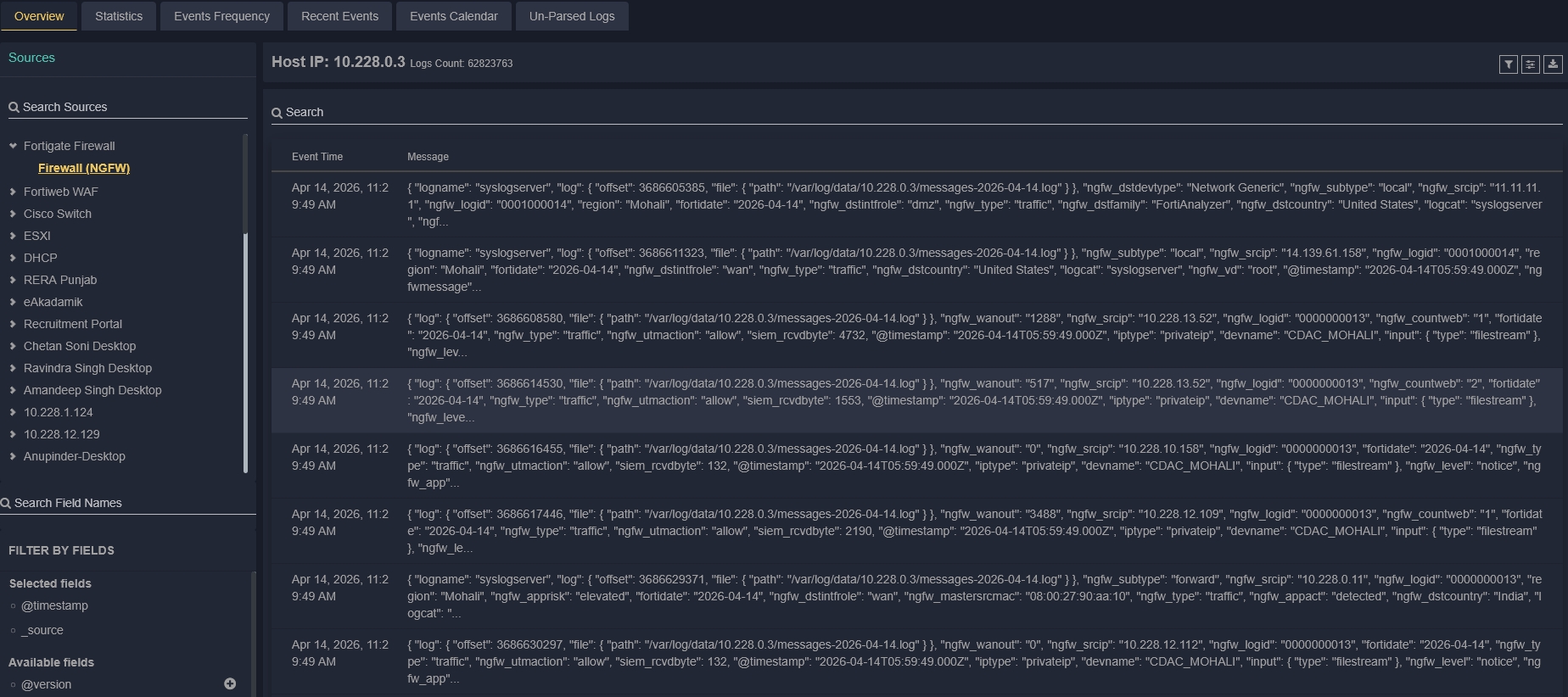
Centralized Log Management
Collect, normalize, and store logs from networks, endpoints, applications, cloud platforms, and security devices in a unified centralized platform for complete visibility.
Enable efficient search, long-term retention, and streamlined forensic investigations to support security operations and compliance requirements.

Automated Incident Response
Automate incident response workflows using predefined playbooks and customizable response actions to minimize manual intervention and reduce operational overhead.
Trigger automated containment actions such as user isolation, IP blocking, and ticket creation to accelerate remediation and improve SOC efficiency.
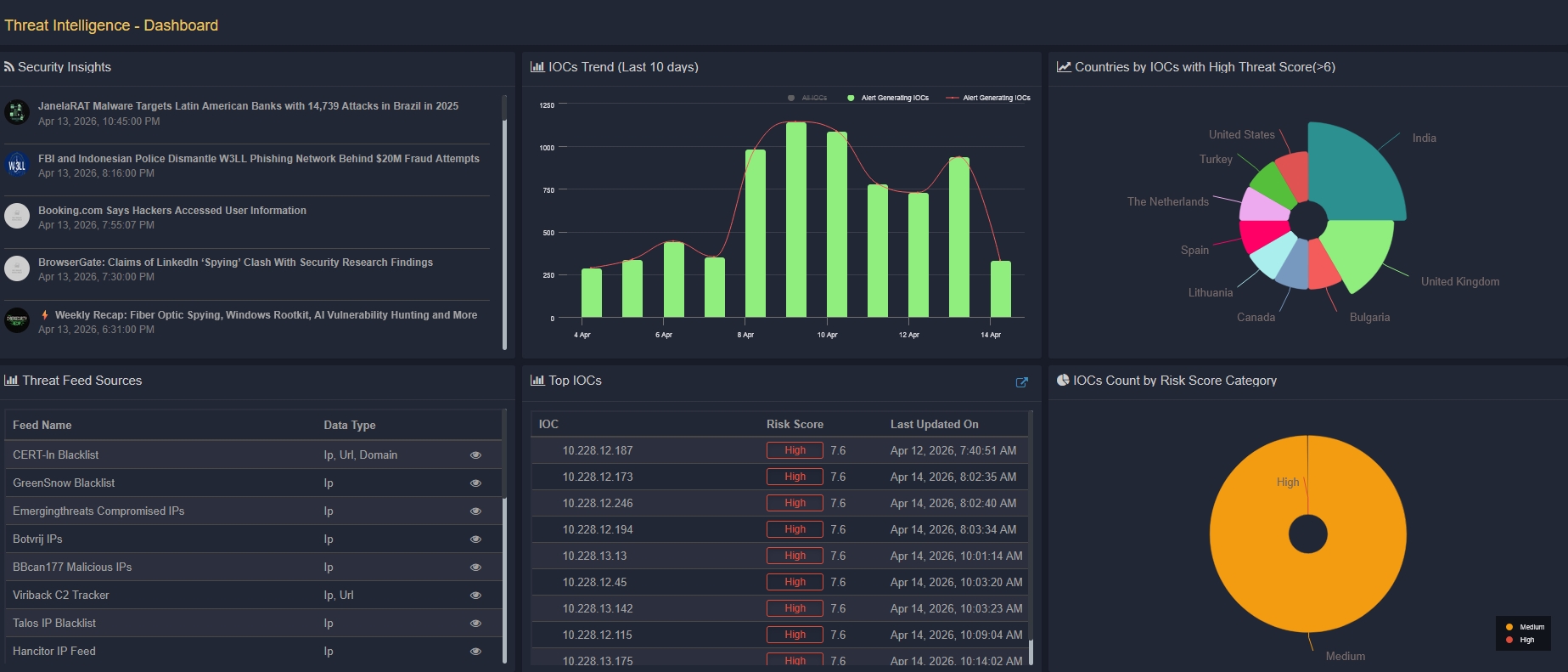
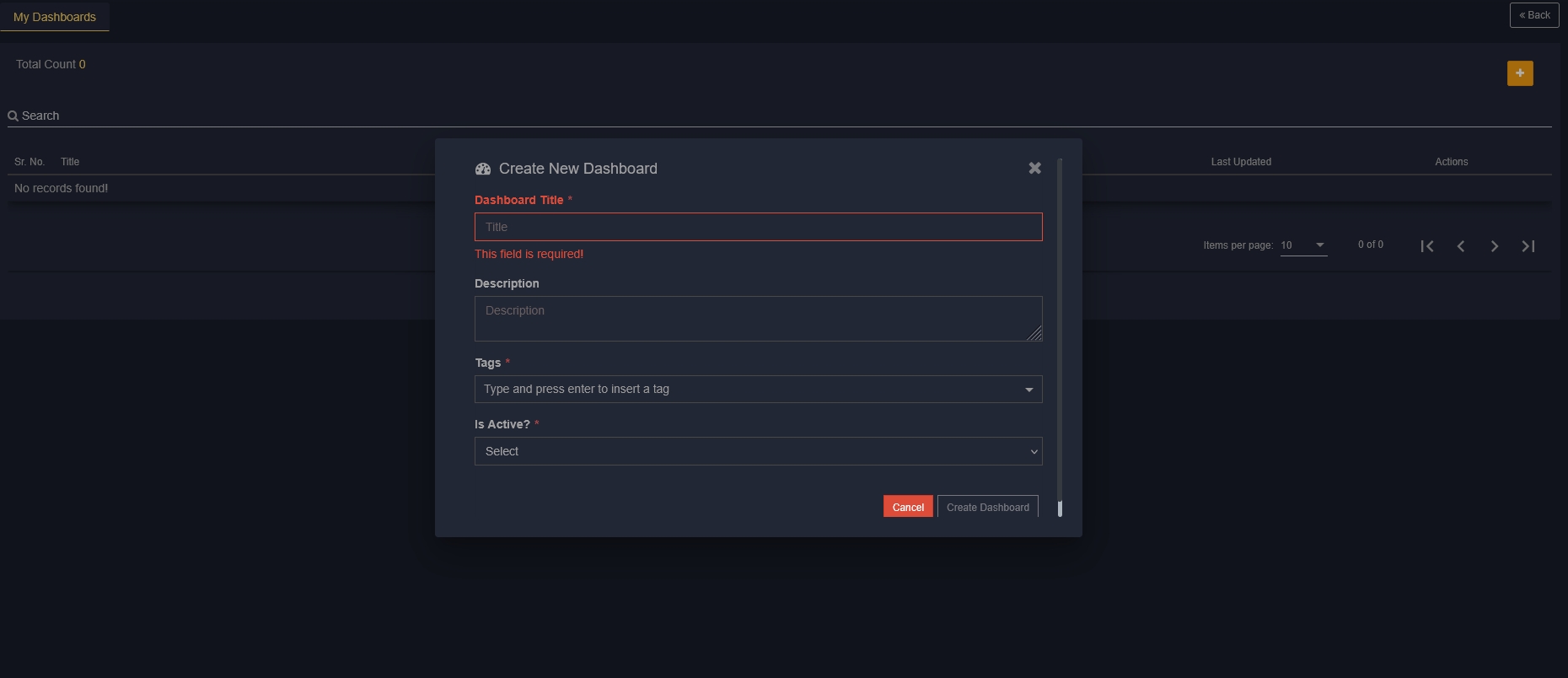
Security Analytics & Dashboards
Gain comprehensive visibility into your security posture through intuitive dashboards, advanced analytics, and real-time visualizations.
Track key security metrics, identify threat trends, and make data-driven decisions with actionable insights tailored for security teams and management.
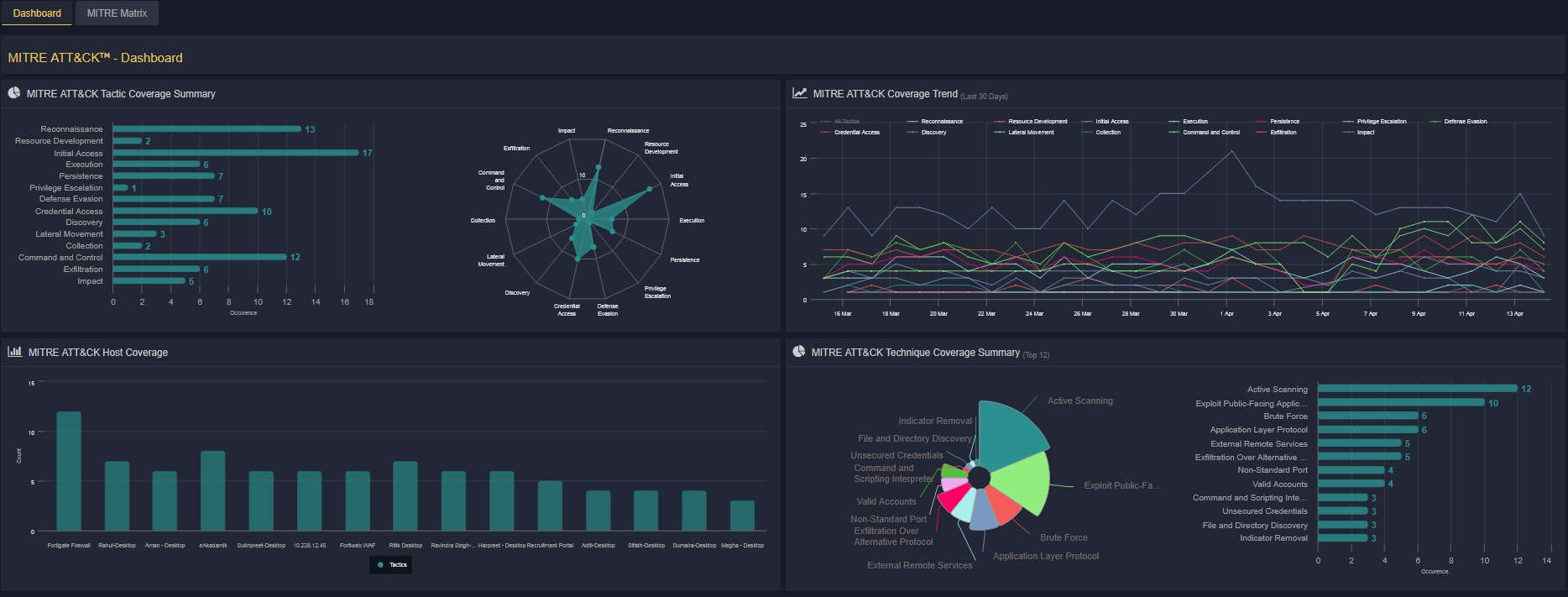
MITRE ATT&CK Mapping
Map detections and alerts to MITRE ATT&CK techniques and tactics to help security teams quickly understand adversary behavior and attack progression.
Identify detection gaps, improve threat coverage, and enhance investigation workflows with structured threat intelligence mapping.
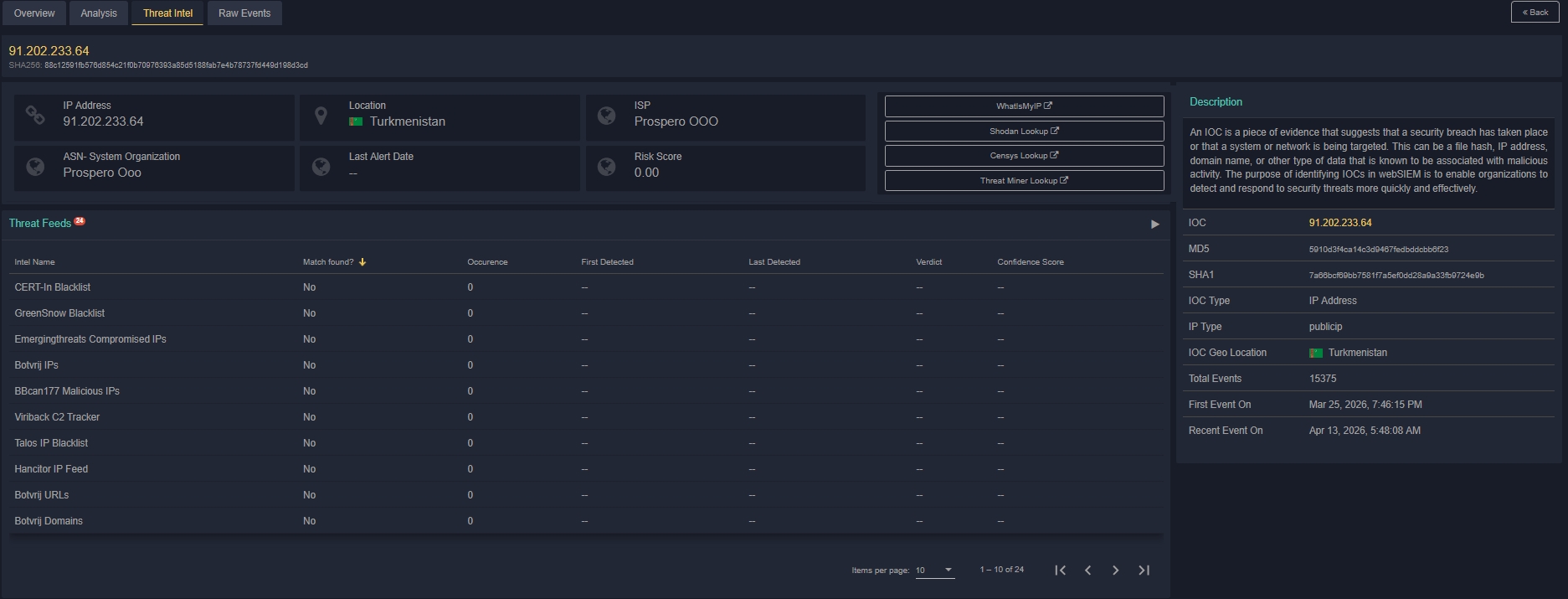
Threat Intelligence Integration
Enhance detection capabilities by integrating global, commercial, and indigenous threat intelligence feeds into your security operations workflow.
Automatically enrich alerts with contextual threat intelligence, helping analysts prioritize risks and respond more effectively to emerging threats.
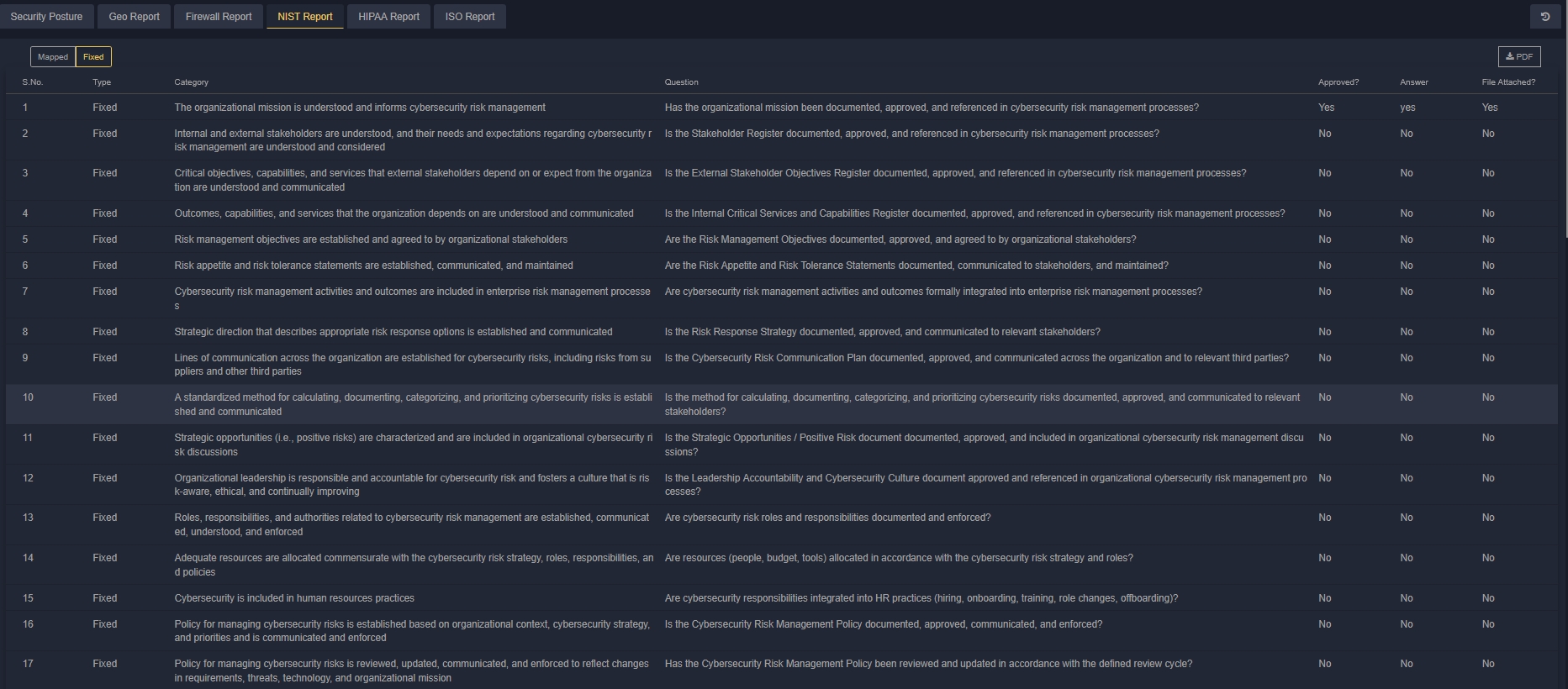
Compliance Monitoring & Reporting
Monitor compliance requirements across multiple regulatory frameworks with automated policy checks and continuous auditing capabilities.
Generate compliance-ready reports, simplify audit preparation, and maintain adherence to industry standards and regulatory requirements.